Cyber incidents rarely begin with sophisticated hacker attacks. More often, they stem from seemingly insignificant gaps in everyday processes: delayed updates, excessive access rights, outdated policies, or inadequate data governance. It is precisely these routine “small issues” that pose the greatest risks to companies — leading to system downtime, financial losses, and reputational damage.
A cybersecurity audit provides a clear, unvarnished view of an organization’s actual security posture. It examines processes, documentation, access management, event monitoring, and incident readiness. In practice, regardless of industry or company size, the same issues tend to surface time and again.
Most companies are confident that their cybersecurity is “generally adequate”: antivirus software is in place, access rights are configured, and the IT department oversees the infrastructure. However, a comprehensive cybersecurity audit conducted in line with international standards often quickly dispels this confidence, revealing the true state of protection.
Audit experience consistently shows that most security incidents are not the result of highly sophisticated attacks, but rather of fundamental process gaps that have gone unnoticed for years. Over time, these weaknesses lead to data breaches, system outages, and tangible financial losses.
Top 7 mistakes identified by cybersecurity auditors
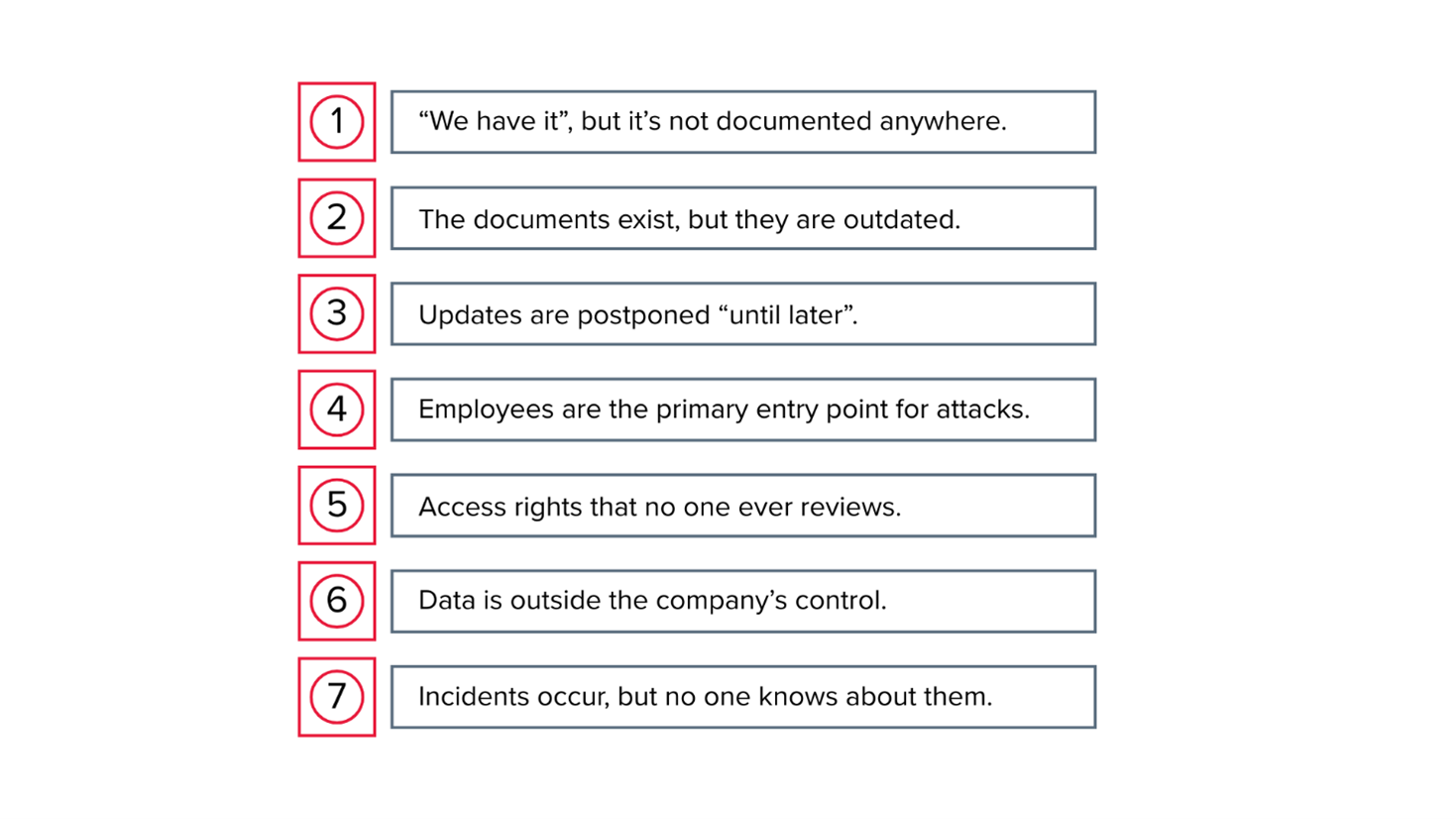
Mistake No. 1. Lack of documented cybersecurity processes (“We have it”, but it’s not documented anywhere)
In many companies, basic information security measures are actually implemented: access is restricted, backups are performed, and system changes are controlled. The problem is that these practices often exist only at the level of informal agreements or personal responsibility of individual specialists, rather than as formally documented policies and procedures.
During a cybersecurity audit, this lack of documentation frequently emerges as a critical vulnerability. Without clearly defined policies, standards, and procedures, there is no consistent approach to security, and key processes become dependent on specific individuals. In the event of an incident, the company is unable to demonstrate that controls actually existed or were applied in a systematic and repeatable manner.
A real‑life example: during an audit at one company, it was found that access to the financial system was considered “controlled.” In reality, access decisions were made at the administrator’s sole discretion, with no documented procedure. As a result, a former employee retained access to critical data for another month after leaving the company.
Mistake No. 2. Outdated and irrelevant information security documentation (The documents exist, but they are outdated)
Having information security policies in place does not necessarily mean they are effective. In many companies, security documentation was created several years ago and has not been reviewed since — despite significant changes to the IT environment. New systems have been introduced, remote work has become common, and cloud services and third‑party providers are now widely used.
As a result, these policies no longer reflect actual processes or address current risks. Such documentation creates only a formal sense of control, while providing little to no real protection.
Case in point: one company’s policy required all data to be stored exclusively on local servers. In practice, however, most files were already being stored in cloud services — without any defined access controls.
These “dead” documents create a dangerous illusion of order.
Mistake No. 3. Lack of regular update and vulnerability management (patch management) (Updates are postponed “until later”)
Patch management is one of the core cybersecurity processes that is consistently underestimated. Updates are often delayed due to concerns about system stability, lack of time, or the absence of clear procedures for testing and deployment.
However, the majority of modern cyberattacks exploit known vulnerabilities for which patches have long been available. Failing to apply updates on a regular basis effectively leaves systems exposed to widely available, well‑documented attack techniques.
Case in point: a widely publicised breach at one company began simply because a server had not been updated for several months. The vulnerability was publicly known, and the attack required nothing sophisticated — just a standard exploit.
Mistake No. 4. Insufficient cybersecurity awareness among employees (Employees are the primary entry point for attacks)
Even the most advanced technical controls cannot ensure security without regular employee awareness and training. Social engineering, phishing, and account compromise remain among the leading causes of cybersecurity incidents.
Without structured and ongoing awareness programmes, employees may use weak passwords, open malicious attachments, or share sensitive information without proper verification. The human factor continues to be one of the most significant cybersecurity risks.
A real-life example: an accountant received an email seemingly “from the CEO,” urgently requesting a financial file. The message appeared credible, and the file was sent — directly to an external attacker.
No security system can compensate for a lack of user awareness if employees do not understand basic cyber risks.
Mistake No. 5. Lack of regular access review and control (Access rights that no one ever reviews)
Access management is one of the most critical components of information security. Yet in many companies, access rights accumulate over years without regular review.
Employees change roles, move between departments, or leave the company, but their accounts and privileges often remain active. This creates significant risks of unauthorised access to sensitive systems and data.
Real‑life example: during an audit, we discovered a user account with administrator privileges that had not been accessed for more than six months. The account remained active and uncontrolled.
This is one of the simplest ways for attackers to gain unauthorised access.
Mistake No. 6. Lack of control over the storage and transfer of corporate data (Data is outside the company’s control)
Without systematic oversight of data, a company loses visibility into where information is stored, who has access to it, and how it is transmitted. The use of personal cloud services, instant messaging apps, and external storage devices often occurs without proper controls.
The absence of data classification policies and DLP (Data Loss Prevention) solutions significantly increases the risk of information leaks and loss of control over critical assets.
Real‑life example: managers stored their client database in personal Google Drives to “make working from home easier.” As a result, the company lost control over sensitive information.
The lack of DLP solutions makes such situations the norm rather than the exception.
Mistake No. 7. Lack of security event monitoring and incident response (Incidents occur, but no one knows about them)
Having logs and technical security tools does not guarantee protection if no one reviews the events. Without systematic monitoring and response processes, attacks can go undetected for weeks or even months.
Effective cybersecurity is not just about preventing attacks—it also requires timely detection of suspicious activity and rapid incident response.
Case in point: a company discovered suspicious activity in its system several weeks after it began. The reason? Logs were collected, but no one analysed them.
Without monitoring and response, any attack has more time to cause damage.
Why is it important?
Most of the issues described above may seem obvious — even “simple.” That is why they are often postponed until the real consequences appear. In practice, however, it is these basic gaps in cybersecurity processes that most frequently lead to serious incidents, downtime, data breaches, and financial losses.
A cybersecurity audit is not just a formal compliance check. It’s a tool for objectively assessing your company’s security posture, identifying weaknesses, and prioritising their remediation — before they can be exploited by attackers.
Robust cybersecurity does not start with expensive technology, but with the fundamentals: clear processes, up‑to‑date documentation, controlled access, effective update management, and regular employee training. Companies that systematically address these basics not only pass audits with greater confidence, but also significantly reduce cyber risks to their business.
Most importantly, it is often much easier — and far less costly — to fix weaknesses during an audit than to deal with the aftermath of a cyber incident.
Are you confident your company is protected?
Order information security services from BDO in Ukraine — we’ll help you safeguard your business, data, and reputation against modern cyber threats.
Cybersecurity solutions from the team of BDO in Ukraine include:
- information security audit (IT audit)
- cybersecurity risk assessment
- cybersecurity systems
- cybersecurity outsourcing
- migration to the cloud